Aegis Fuzzer
ICS/SCADA applications require robust components, but too often software is the weakest link.
Aegis is a smart fuzzer for power system protocols that can identify robustness and security issues in communications software before it is deployed in a production system.
View Documentation Contact Us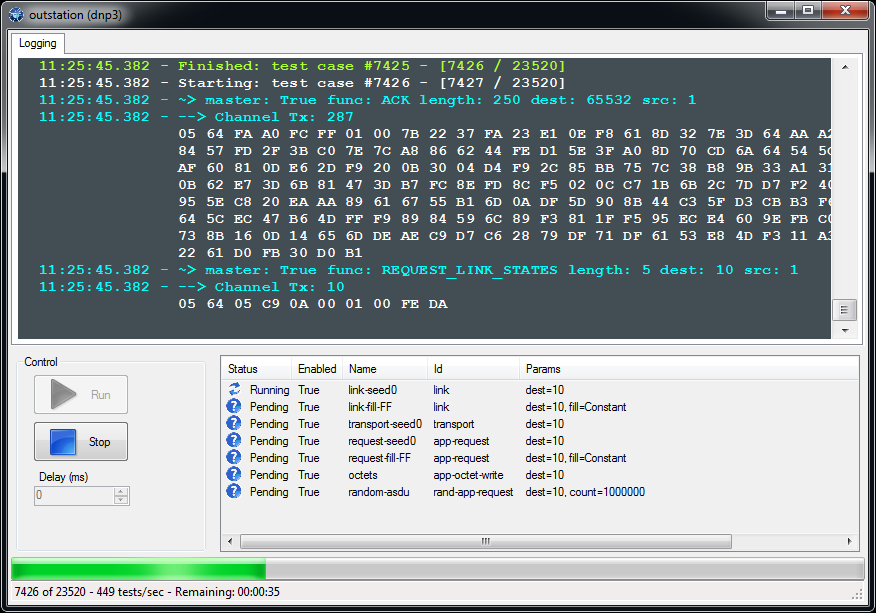
High-value Testing
Aegis has proven results but costs a fraction of the price of other ICS fuzzing products. We license Aegis for the following use cases:
- Vendors seeking to eliminate defects from their products
- Asset owners auditing their equipment
- Pentesters or 3rd-party security personnel doing assessments
Model-based
Aegis is a protocol-aware smart fuzzer and generates malformed messages that are much more likely to identify defects than random fuzzing.
Easy to Use
Since Aegis understands each protocol, little user configuration and experience are required to operate the tool.
Automated Testing
The GUI for Aegis makes user-driven testing easy, however, the same tests are also available from the command line allowing for full test automation.
| Protocol | Server (outstation) | Client (master) |
|---|---|---|
| DNP3 (IEEE-1815) | ||
| Modbus TCP | ||
| IEC 60870-5-104 |
Licensing
Aegis™ is licensed on a per-seat subscription basis with a term of typically one year. Enterprise-wide licensing that grants unlimited seats is also available. Discounts are available for trainers, academia, and asset owners.
Contact UsLearn More About Fuzzing
Browse some of our posts about fuzzing and secure programming.
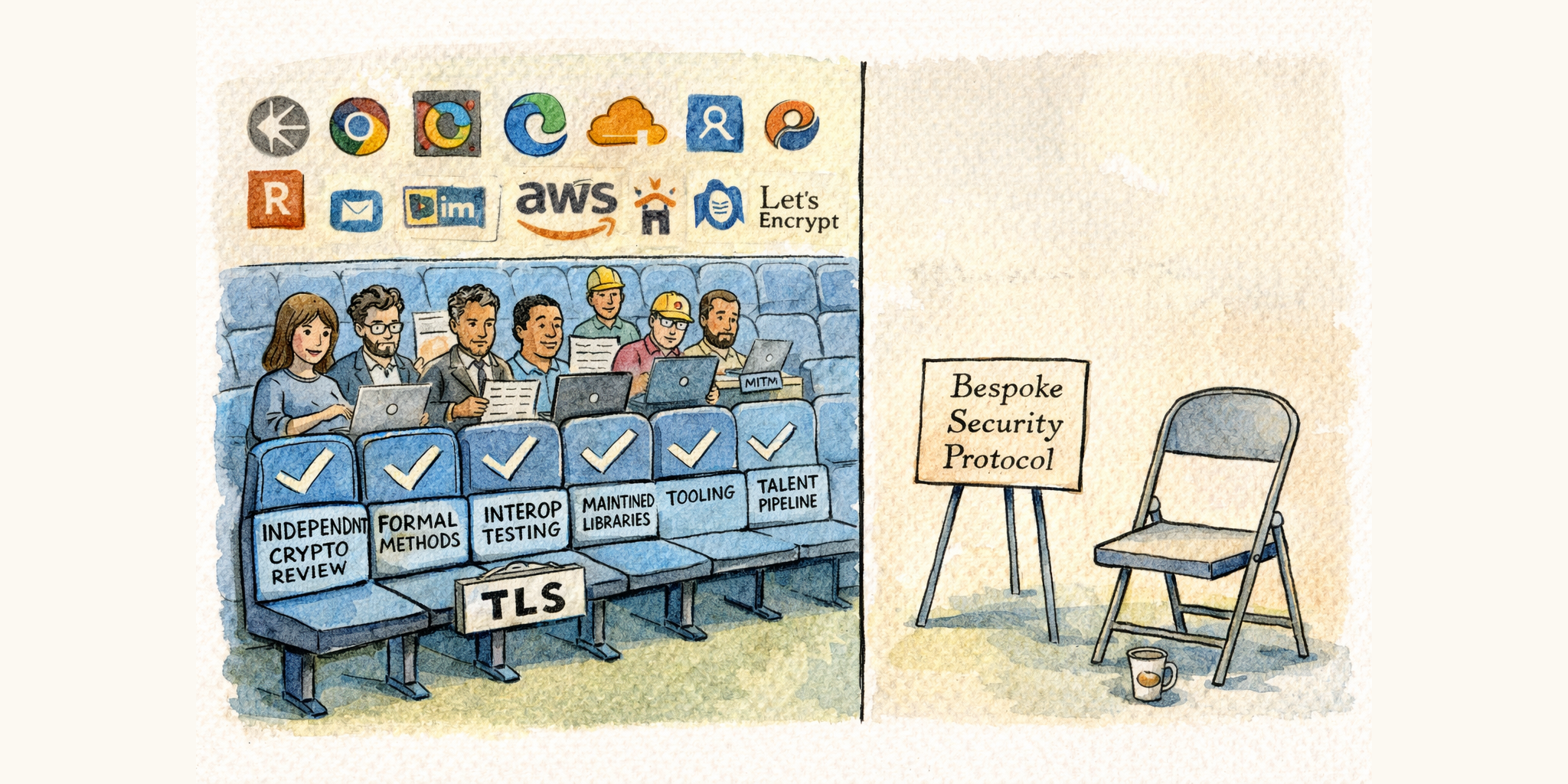
The Case Against DNP3 SAv6 and AMP
Read MoreDNP3’s new security protocol reinvents what TLS already provides, and it will be implemented by vendor teams that have historically struggled to safely parse basic DNP3 messages. Use TLS. It’s proven, audited, and your developers don’t need to be cryptographers.
Battalion Energy
I’m pleased to announce that I’ve joined Battalion Energy as cofounder and CTO. We’re building a cloud + edge controls platform focused on battery energy storage.
There are so many things that excite me about this venture:
- Extremely talented founding team with a track record of building Awesome Things™.
- Building a modern and secure controls platform using 🦀Rust🦀 and webassembly!
- Disruptive business model in a rapidly expanding market.
- Company focus on open APIs, open ecosystems, and playing nice with others.

Protocol Scalability
Building systems that scale is becoming critically important as the power grid undergoes a rapid transformation to meet the challenge of renewables and climate change. Software architecture is crucial to scaling communications solutions for emerging applications like distributed energy resources (DERs).
This blog post discusses how software architecture affects the scalability of communication protocols and provides performance data for our protocol offerings.
Read More